
80% of user time spent in browsers
Research, Email, SaaS apps, Productivity
44% of cyber attacks involve the browser
Phishing, ClickFix, Downloads, Shadow AI
Browsers are where most work happens - and where security is the weakest
Sekant secures the browser
Sekant is a lightweight extension that embeds runtime intelligence directly in browsers - giving visibility and control where traditional tools cannot.
SUPPORTED BROWSERS
Chrome
Edge
Firefox
Brave
Opera
Safari
(Coming soon)
How does Sekant work?
Deploy Extension
Push to managed browsers via MDM or allow employees to self-install. Takes seconds.
Monitor & Analyze
Sekant continuously analyzes pages, scripts, and user actions using on-device AI.
Block & Alert
Threats are neutralized in real-time. Admins get visibility through centralized dashboards.

Key features
Runtime Visibility
See what happens inside the browser in real-time, not just at the network perimeter
Personalized
AI models self-adapt to each user's unique browsing patterns for tailored protection
Complete Privacy
All analysis happens locally – no sensitive data ever leaves the browser
Scalable
Operates on edge devices – no network load or server infrastructure required
Embedded AI Detection
On-device intelligence analyzes page content, scripts, and behavior patterns instantly
Zero Latency
Protection at the point of click, before damage occurs
Use Cases
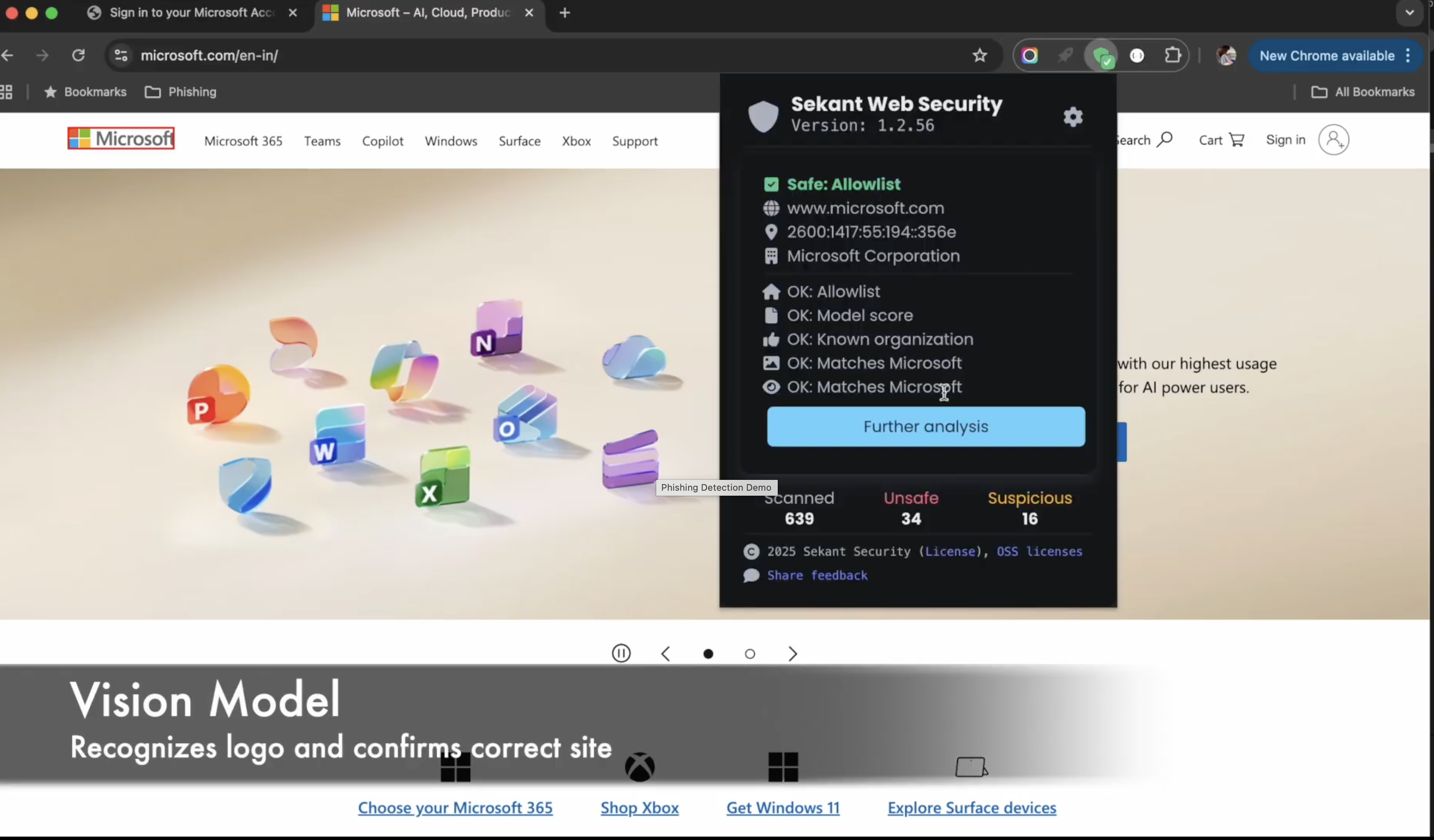
Phishing Detection
The Problem
- AI phishing is 4.5× more effective than human-crafted attacks.
- Campaigns can be created in minutes, not hours.
- Attacks now span SMS, social, and messaging apps, bypassing email security.
- User training alone isn’t enough.
Sekant's Solution
- Real-time page analysis of DOM, scripts, forms, and visuals.
- AI detects credential harvesting, brand impersonation, and social engineering.
- Protects across email, SMS, social, QR codes — anything in a browser.
- Blocks threats before credentials are entered.
YOUR OUTCOME
85% Zero-Day Detection Rate
Near-complete elimination of successful phishing attacks, irrespective of initial channel
ClickFix Detection
The Problem
- AI-generated phishing campaigns are 4.5X more effective at getting clicks than human-crafted attempts (Microsoft Research)
- Attackers can now create convincing campaigns in 5 minutes with 5 AI prompts – matching what took experts 16 hours (IBM)
- Multi-channel attacks via SMS, social, and messaging apps bypass email-focused security entirely
- User training shows limited effectiveness – UC San Diego study of 20,000 employees showed no marked improvement
Sekant's Solution
- Real-time page analysis examines DOM, scripts, forms, and visual elements at the moment of access
- AI models detect credential harvesting patterns, brand impersonation, and social engineering tactics
- Works across all channels – email links, SMS, social media, QR codes – anything that opens in a browser
- Blocks threats before credentials can be entered, not after the damage is done
YOUR OUTCOME
97% Detection Rate
Complete protection against attack vector that bypasses traditional defenses
Demo Video
Block Unsafe Downloads
The Problem
- Drive-by downloads inject malware without user interaction
- Malicious files disguised as legitimate software updates or documents
- Personal cloud storage and file-sharing sites bypass corporate controls
- Traditional solutions only scan after download; too late to prevent execution
Sekant's Solution
- Embedded YARA scanning engine analyzes file content before execution
- Admins configure custom rules describing unsafe file patterns
- Real-time reputation checking against known malicious domains
- Policy controls allow enterprises to restrict download sources
YOUR OUTCOME
Configurable Download Policies
Content blocking rules tailored to your organization’s specific threat landscape
Demo Video
Shadow AI Monitoring
The Problem
- Employees paste sensitive data into unauthorized AI tools daily
- No visibility into what data is being shared with external AI services
- Compliance and IP protection policies are impossible to enforce
- Blocking all AI tools hurts productivity – but allowing them creates risk
Sekant's Solution
- Logs prompts, data pastes, and file uploads to AI platforms
- Warns users when pasting or uploading data to unsanctioned AI tools
- Automatic detection of online LLM chatbots – not just list-based blocking
- Full audit trail for compliance and security investigations
YOUR OUTCOME
Complete Visibility
Enterprises gain full insight into AI tool usage and can enforce data protection policies
Demo Video
Fleet-wide Visibility
The Problem
- Drive-by downloads inject malware without user interaction
- Malicious files disguised as legitimate software updates or documents
- Personal cloud storage and file-sharing sites bypass corporate controls
- Traditional solutions only scan after download; too late to prevent execution
Sekant's Solution
- Embedded YARA scanning engine analyzes file content before execution
- Admins configure custom rules describing unsafe file patterns
- Real-time reputation checking against known malicious domains
- Policy controls allow enterprises to restrict download sources
YOUR OUTCOME
Centralized Dashboard
Full fleet-wide visibility into browser security posture across all endpoints
Demo Video